The First 24 Hours After a Cyberattack: What Actually Happens?
Most businesses think about cybersecurity in terms of prevention. Firewalls. Antivirus. Training.
But the real test isn’t whether something gets through.
It’s what happens after it does.
Because in the first 24 hours of a cyberattack, the difference between a controlled incident and a full business disruption comes down to a handful of decisions made quickly.
Here’s what that actually looks like.
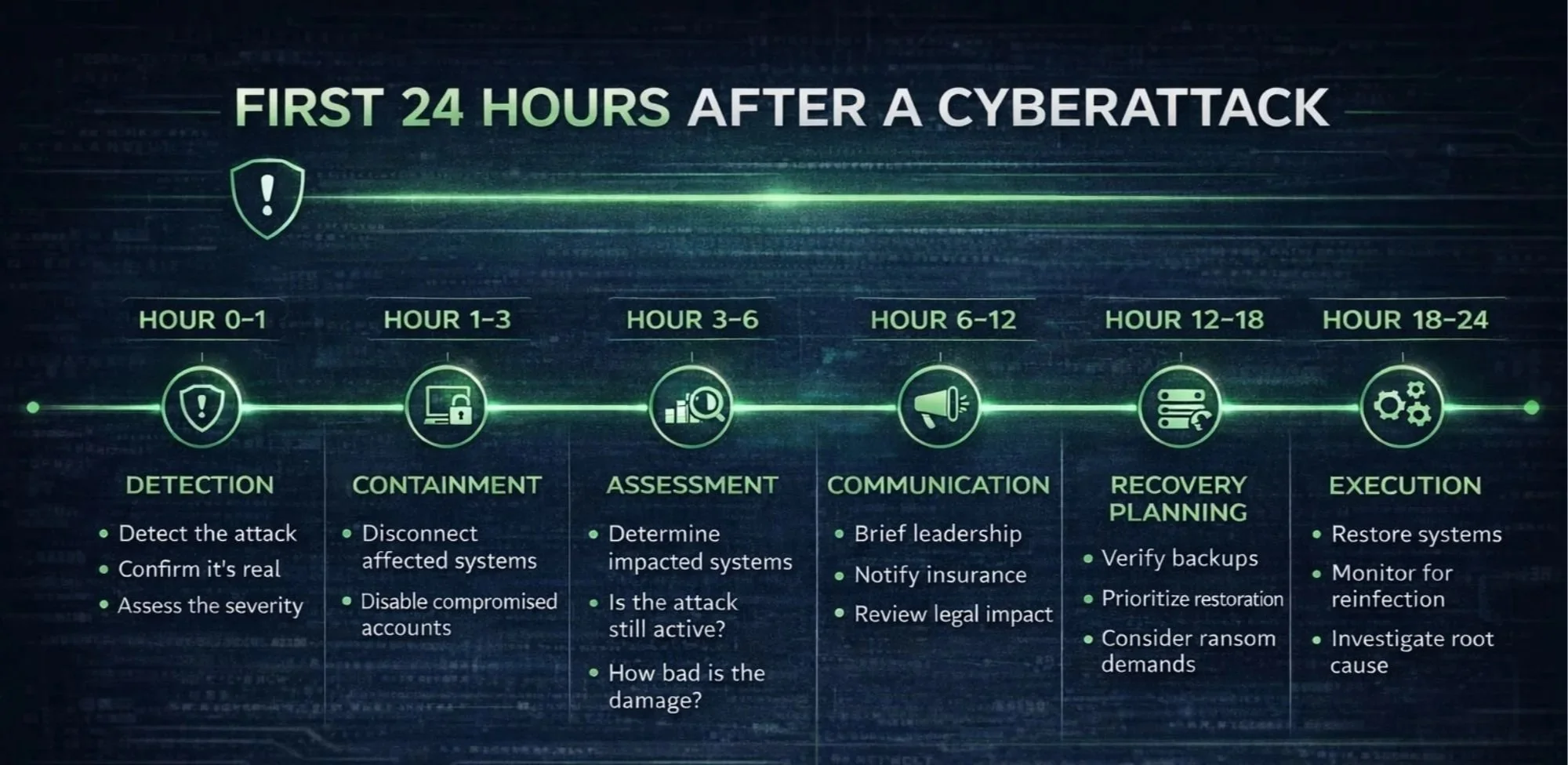
Hour 0–1: Detection (or Realization)
The attack is discovered.
Sometimes it’s obvious:
Systems locked with a ransom note
Files suddenly inaccessible
Other times, it’s subtle:
Suspicious login alerts
Unusual system behavior
A vendor or employee reporting something off
Key decision: Is this a false alarm or the start of something real?
Delaying here is common. Confirming matters. But, so does acting quickly.
Hour 1–3: Incident Containment
Once an incident is confirmed, the priority shifts immediately to stopping the spread.
This may include:
Disconnecting affected systems
Disabling compromised accounts
Blocking suspicious activity at the network level
This is where hesitation can make things worse.
Key decision: Do we isolate systems immediately even if it disrupts operations?
In most cases, the answer is yes.
Hour 3–6: Initial Assessment
With the immediate threat contained (or at least slowed), the focus turns to understanding:
What systems are affected?
Is data encrypted, accessed, or both?
Is the attack still active?
At this stage, information is incomplete.
That’s normal.
Key decision: Do we bring in outside expertise (security team, forensics, legal)?
Waiting too long to escalate can limit your options later.
Hour 6–12: Communication and Control
Now the situation becomes broader than IT.
Internal communication starts:
Leadership is briefed
Employees are given instructions
Systems access may be restricted
External considerations begin:
Legal and compliance review
Vendor involvement
Public/DoD reporting considerations
Key decision: Who needs to know? And, how much do we say right now?
Over-communicating can cause confusion. Under-communicating creates risk.
Hour 12–18: Recovery Planning
At this point, the focus shifts from reaction to recovery.
Are backups available and usable?
How long will restoration take?
What systems come back first?
This is where preparation (or lack of it) becomes very clear.
Key decision: Do we restore from backups or consider other options?
This is also where discussions around ransom demands sometimes begin.
Hour 18–24: Execution Begins
Recovery response starts taking shape.
Systems begin to be restored
Access is gradually reintroduced
Monitoring is increased to prevent reinfection
At the same time:
Documentation begins for insurance and compliance
Root cause analysis is underway
Key decision: How do we bring systems back online safely without repeating the problem?
Moving too fast can undo progress. Moving too slow extends downtime.
What Separates a Controlled Incident From a Crisis
It’s not luck.
It’s preparation.
The businesses that handle cyberattacks well tend to have:
Clear access control
A defined incident response process
Someone accountable for leading the response
Not because they expected an attack but because they planned for one.
A Better Way to Think About Cybersecurity
Instead of asking: “How do we prevent an attack?”
A more practical question is: “If something happened tomorrow, would we know exactly what to do?”
That’s what determines how the first 24 hours go.
Cyberattacks are Disruptive
But they don’t have to be chaotic.
With the right preparation, the first 24 hours can be structured, controlled, and focused on recovery—not reaction.
And that makes all the difference.